Anonymous Content
Table of Contents
Anonymous Content: Navigating the Realm of Unattributed Creations
Anonymous content—any message, article, review, artwork, or commentary published without your real-world identity attached—is not a niche phenomenon. It is a foundational element of modern digital discourse. Whether you are a whistleblower, a survivor sharing a story, a political dissident, or simply someone who values privacy, the ability to create and consume unattributed content safely is a critical skill. This guide is designed for anyone who needs to understand the full landscape: how to protect your identity, what “content privacy” truly means, how to publish without leaving a trail, and how to evaluate anonymous claims responsibly. You will learn the practical steps to prevent doxxing, account linkage, and metadata leaks, as well as the ethical and legal frameworks that separate responsible anonymity from reckless behavior. The goal is not to encourage hiding, but to empower safe, truthful, and impactful expression. By the end, you will have a concrete, actionable system for navigating the realm of unattributed creations with confidence and integrity.
Understanding Anonymous Content: More Than Just Hiding a Name
Anonymous content is any creation shared without a publicly verifiable link to the author’s real-world identity. This can range from a pseudonymous blog with a consistent pen name to a one-off comment on a forum with no profile at all. The key distinction is unlinkability: the degree to which someone can connect your online activity to your physical self. This is not a binary state—it exists on a spectrum. A pseudonym that you use across multiple platforms with the same email address is far less anonymous than a single-use account on a Tor-based forum.
The reasons for seeking anonymity are diverse and often deeply practical. People publish unattributed content to protect themselves from professional retaliation, social stigma, or physical harm. They do it to report workplace misconduct, discuss sensitive health issues, or engage in political speech in repressive environments. For content creators and marketers, understanding this motivation is crucial. Anonymous audiences are not untrustworthy; they are often the most cautious and discerning. They evaluate content based on evidence, consistency, and community reputation rather than an author’s name or credentials. This shifts the burden of proof onto the creator, demanding higher standards of truthfulness and sourcing.
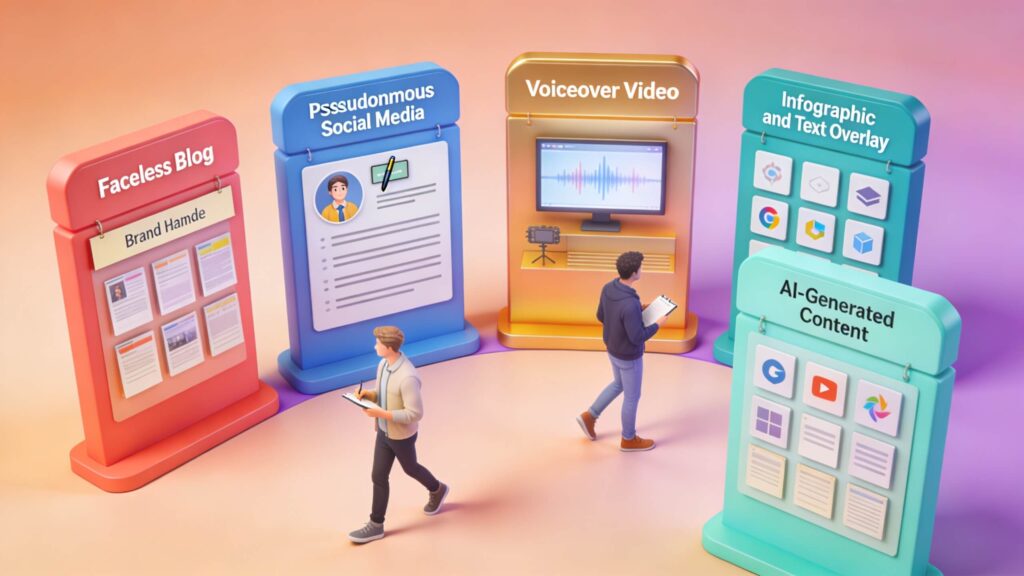
From a search engine optimization perspective, anonymous content presents unique challenges. Trust signals like author bios and social proof are absent. Success depends on the quality of the writing, the depth of research, and the ability to build a consistent narrative over time. For a deeper dive into the technical side of online privacy, the EFF’s privacy resources provide an excellent starting point for understanding how platforms track users through cookies, device fingerprints, and IP addresses.
Protecting Your Identity: The Threats You Must Plan For
Most people think protecting anonymity is about not using their real name. In reality, the most common de-anonymization paths are subtle and cumulative. A solid identity protection strategy treats anonymity as a system, not a single toggle. You must plan for threats that exploit patterns, not just explicit disclosures.
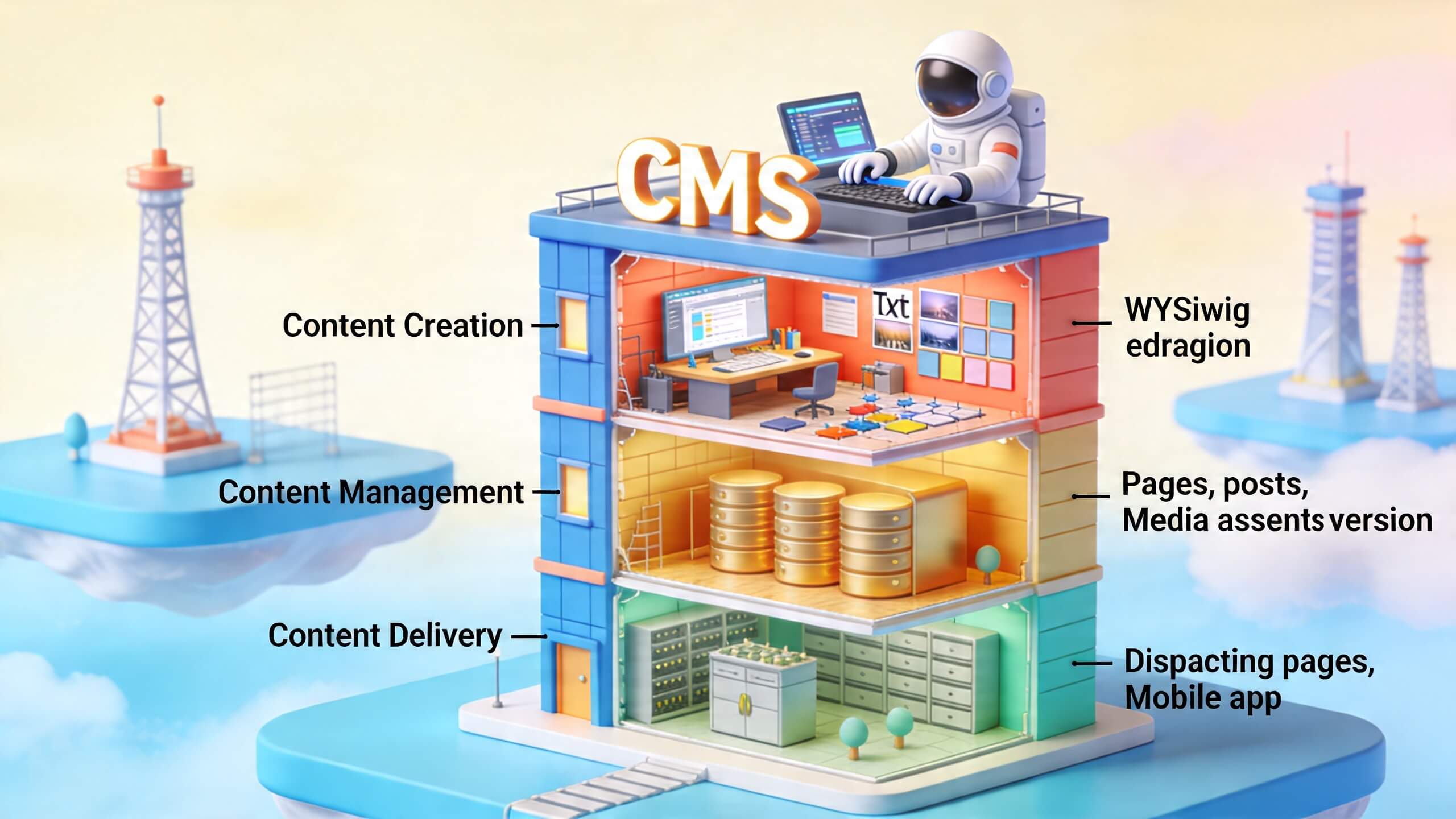
Content Privacy vs. Identity Privacy
These two concepts are often confused, but they require different defenses. Identity privacy is about preventing linkage between your online activity and your real-world self. Content privacy is about preventing unauthorized access to what you create, including drafts, unpublished posts, and private messages. A common mistake is focusing entirely on identity while leaving content exposed through insecure hosting, metadata in uploaded files, or drafts stored in a personal cloud account that is linked to your real name. Both must be protected in tandem.
Common De-anonymization Paths
Understanding how people get discovered is the first step to preventing it. The most frequent paths include:
- Account linkage: Using the same email address, phone number, or recovery method across anonymous and personal accounts is the single most common leak. A password reset request sent to your personal email can undo years of careful anonymity.
- Network traces: Your IP address is a direct link to your internet service provider and, often, your physical location. Even if you use a pseudonym, your IP can be logged by platforms and exposed through legal requests or data breaches.
- Device fingerprints: Your browser and operating system create a unique signature based on installed fonts, screen resolution, time zone, and other characteristics. This fingerprint can be used to track you across sessions even if you clear cookies.
- Metadata leakage: Photos, documents, and screenshots often contain hidden data like GPS coordinates, camera model, creation dates, and author names. Failing to strip this data before uploading is a common and preventable error.
- Behavioral patterns: Your posting times, writing cadence, vocabulary choices, and the specific topics you cover can create a behavioral profile that matches your known identity. If you only post between 2 AM and 4 AM on weekdays, that pattern narrows the search space significantly.
For a more technical exploration of these threats, the Tor Project’s documentation offers detailed explanations of how network-level tracking works and how to mitigate it.
Content Security: Encryption, Backups, and Safer Workflows
Even if you publish anonymously, the security of your pre-publication work is paramount. Think like an incident responder: if someone obtained your device or intercepted your connection, what could they learn? The goal is to minimize the blast radius of any single compromise.
Use Encryption Where It Matters
Encryption protects data both in transit and at rest. For private messaging, use end-to-end encrypted tools. For sensitive drafts, store them in an encrypted container or use a service that offers client-side encryption. For general connection privacy, the Tor browser is the gold standard for reducing straightforward IP tracking, though no tool is perfect. For a broader understanding of encryption best practices, the Surveillance Self-Defense guide from the EFF provides actionable, step-by-step instructions.
Reduce Draft Exposure
A common and devastating mistake is writing a sensitive draft in a personal cloud account (like Google Docs or Dropbox) and then copying it into an anonymous platform. If that draft exists in a logged, synced, and backed-up account, it may be recoverable through legal requests, account compromise, or even accidental sharing. Safer workflows include:
- Writing drafts in a privacy-focused environment: a separate browser profile dedicated to anonymous work, a separate storage account that is not linked to your real identity, or offline draft editing on a device that is not connected to your personal accounts.
- Removing metadata from files before upload. Tools like ExifTool can strip EXIF data from images and documents.
- Using secure deletion for sensitive local files after posting. Standard deletion often leaves recoverable traces on your hard drive.
Anonymous Posting: Practical Steps to Prevent Accidental Disclosure
Anonymous posting is where most leaks happen—not because of sophisticated hacking, but because of small, preventable oversights. Your goal is to eliminate obvious identifiers and reduce linkability across your digital footprint.
What to Avoid
- Posting from a logged-in personal account on the same device. This is the digital equivalent of wearing a name tag while wearing a mask.
- Including real-world details that only your circle can connect to you. This includes company nicknames, unique project names, specific dates tied to your personal life, or descriptions of events that only a few people witnessed.
- Uploading images or screenshots without checking metadata. A single photo with embedded GPS data can reveal your home address.
- Using the same phrasing, vocabulary, or rhetorical patterns you use elsewhere publicly. If your writing style is distinctive, it can be matched through stylometric analysis.
Protected Identity Basics
Creating a protected identity requires more than a different username. It requires a complete separation of digital infrastructure. Use a separate email address and account recovery flow that does not connect to your real identity. Consider using a separate device or at least a dedicated browser profile so cookies, cache, and device fingerprints do not cross over. Apply the principle of least linkage: the less shared identity data between your personal and anonymous selves, the harder it is for anyone to connect them.
Secure Channels for Anonymous Content: Tools and When to Use Them
Secure channels are the infrastructure that reduces tracking and interception. The right choice depends on your specific threat model: are you worried about platform profiling, local surveillance, or a targeted investigation by a sophisticated adversary?
Anonymous Networks (Tor, I2P)
Anonymous networks like Tor route your traffic through multiple relays, making it difficult to link the source of a connection to its destination. Tor is the most widely used and is effective at preventing websites from seeing your real IP address. I2P is another option, designed for peer-to-peer applications and offering different anonymity properties. These networks are essential for publishing content that must not be traced back to your physical location.
Protected Identity via VPNs
A VPN can mask your IP address from many websites and encrypt traffic between you and the VPN provider. However, a VPN shifts trust to the provider. They can see your real IP address and the destination of your traffic. Choose a provider with a clear, audited no-logs policy and avoid “free VPN” models that monetize user data. For most users, a VPN is a good complement to other privacy tools but should not be relied upon as a sole defense.
Anonymous Browsing and Tracker Reduction
Browser-level protections help reduce third-party tracking and limit the chance of linkability. Use privacy-focused browser settings, enable tracker blocking, and enforce strict cookie controls. For a comprehensive list of tools and techniques, the Privacy Tools guide offers a well-maintained directory of privacy-respecting software and services.
Featured Snippet: How to Share Anonymous Content Safely (Quick Checklist)
Anonymous content safety means publishing without exposing personal identifiers while reducing tracking and metadata leaks. Use the steps below to lower your risk:
- Separate identities: Create a new email and account recovery method that isn’t tied to your real identity. Never use the same phone number or backup email.
- Reduce device linkage: Use a separate browser profile (or separate device) so cookies, logins, and device fingerprints don’t mix with your personal accounts.
- Secure the connection: Use Tor or a reputable VPN based on your threat model. For maximum privacy, use Tor for publishing and a VPN for general browsing.
- Remove metadata: Check images and documents for EXIF and hidden fields before uploading. Use a metadata stripper tool.
- Avoid unique identifiers: Omit specific employer names, exact dates, and details only your circle would recognize. Generalize where possible.
- Use privacy-first publishing: Write drafts offline or in a separate secured environment, then publish. Do not draft in a personal cloud account.
The Power of Anonymous Blogging: When Privacy Enables Better Truth
Anonymous blogging is one of the most durable forms of unattributed content because it supports continuity. An author can build an archive, refine arguments, and earn reader trust over time without ever revealing their identity. This matters in niches where people need time to process events, where speaking publicly could lead to retaliation, or where the author’s identity might bias the reception of the information.
Contrary to intuition, anonymous blogs can be a credibility advantage in specific contexts. When a writer has no brand to protect and no sponsorship to please, readers may assume the author is less influenced by external incentives. This is not always true—anonymous authors can still be biased or fraudulent—but the format forces readers to evaluate evidence and consistency across posts rather than relying on the author’s name. This creates a more rigorous information environment.
Mini Case Study: Workplace Misconduct Reporting
Consider a common scenario: an employee wants to document patterns of misconduct but fears retaliation. If they publish under a pseudonym and carefully avoid revealing the company name or specific individuals, they can still provide concrete timelines, describe processes, and share supporting documents with metadata removed. Over time, the blog can become a reference point for journalists, investigators, or community members. The key is that the author must protect not only themselves, but also any victims or witnesses by removing identifying details. This illustrates a critical lesson: even anonymously, trust is built on verifiable structure. You can publish redacted receipts and clearly separate what is confirmed from what is alleged.
Anonymous Content and Freedom of Speech: The Upside and the Edge Cases
Anonymous content can strengthen freedom of speech by reducing the fear of retaliation. People who might otherwise stay silent—because of stigma, safety concerns, or social power imbalances—can share experiences and opinions. Historically, anonymity has played a vital role in social movements, whistleblowing, and political dissent where exposure could lead to harm. The ACLU’s resources on free speech provide a broad legal context for understanding the protections and limits of anonymous expression.
However, freedom of speech is not freedom from consequences. Platforms and governments may remove illegal content or pursue civil claims in cases of defamation, harassment, or copyright infringement. Even where speech is legal, communities may apply moderation policies to protect users. The tension between open expression and accountability is a defining challenge of the internet.
What Anonymous Environments Amplify
- Marginalized perspectives: Stories that are ignored when only mainstream identities are heard can find an audience.
- Whistleblowing and accountability: Reports that would be too risky under real names can surface critical information.
- Rapid debate: High volume of claims and counterclaims, often without the usual filters of editorial oversight.
The Edge Cases: Misinformation and Harmful Speech
Anonymous settings can also produce unverified claims that spread quickly. Without identifiable accountability, some users treat anonymity as a license to exaggerate or fabricate. Others target individuals with harassment. The risk increases when anonymity intersects with algorithms that reward engagement over accuracy. As a consumer, adopt a verification mindset: look for primary sources, cross-check dates, and treat emotionally persuasive narratives as a starting point, not a conclusion.
Balancing Anonymity and Responsibility: A Creator’s Ethical Framework
The most sustainable anonymous creators follow an internal code of responsibility. Their anonymity does not erase the impact of their words. If your content could harm someone, you should assume the harm is real even if you cannot see it. This is not about censorship; it is about proportionality and respect.
Use Harm-Minimization Instead of “Anything Goes”
- Consent matters: Do not publish details about private individuals without permission, even if you think they cannot be identified. The risk of re-identification is often higher than you assume.
- Be careful with accusations: Clearly separate facts, observations, and allegations. Use language that reflects the level of certainty you have.
- Respect privacy boundaries: Avoid doxxing-style details like addresses, personal phone numbers, or workplace schedules. Your right to speak does not override someone else’s right to safety.
- Correct mistakes: Anonymity should not prevent accountability. Update or retract when evidence changes. A willingness to admit error builds long-term trust.
Responsible Engagement as a Strategy
Responsible behavior is not just ethical; it is strategic. Anonymous creators who avoid hate, harassment, and misinformation are more likely to build a loyal audience and avoid platform bans. For brands and digital marketing teams, this is crucial: if you manage communities, “safe anonymity” is part of your reputation and compliance posture. It protects your platform from legal liability and fosters a healthier environment for all users.
Legal and Ethical Considerations of Anonymous Content
Legal risk is context-dependent, but certain issues recur across jurisdictions. Anonymous content can still trigger liability if it violates laws or platform rules. Understanding these boundaries is not optional for serious creators.
Legal Considerations to Understand
- Defamation: False statements presented as fact that harm someone’s reputation are not protected by anonymity. You can be sued for defamation even if you publish under a pseudonym.
- Copyright: Reposting copyrighted material without permission, even under a pseudonym, is infringement. Fair use is a defense, but it is not automatic.
- Harassment and threats: Content that targets individuals or incites violence is illegal in most jurisdictions. Anonymity does not shield you from prosecution.
- Privacy violations: Publishing private information without consent (like medical records or financial data) can lead to civil and criminal penalties.
- Regulated content: Certain industries face additional rules. Giving medical, financial, or legal advice anonymously may violate professional licensing laws.
Because laws vary widely, consult a qualified attorney if you are operating at scale or dealing with sensitive allegations. For general legal literacy, the Cornell Legal Information Institute offers a reliable overview of defamation, privacy, and other relevant concepts.
Ethical Considerations You Can Apply Immediately
- Truthfulness: Do not “fill gaps” with assumptions presented as certainty. If you are unsure, say so.
- Proportionality: Do not share more private detail than necessary to make your point. The more specific you are, the higher the risk of harm.
- Verification: Cite sources, link to documents where safe, and explain uncertainty. Your credibility depends on your evidence.
- Community impact: Assume your post can be screenshotted and redistributed. Write for a permanent audience, not a temporary one.
Anonymous Content and Online Communities: How Dynamics Change
Anonymous content changes group behavior. It can increase openness, but it can also reduce accountability. The net effect depends on community design: moderation quality, reporting systems, and clear norms. Understanding these dynamics is essential for anyone who manages or participates in online communities.
Benefits for Communities
- Lower fear barrier: Users share problems they might otherwise hide, leading to richer discussions and more honest feedback.
- More diverse participation: People from different backgrounds feel safer contributing, increasing the range of perspectives.
- Faster feedback: Readers can respond without worrying about social consequences, leading to more candid exchanges.
Risks for Communities
- Toxic behavior: Anonymity can embolden harassment, trolling, and hate speech.
- Factionalism: Groups may form around rumor and ideology rather than evidence, leading to echo chambers.
- Moderation overload: High volume of content makes it harder for moderators to respond quickly and fairly.
Challenges of Moderating Anonymous Content (and What Works)
Moderating anonymous content is difficult because you cannot easily enforce accountability at the individual identity level. Still, you can enforce behavior. The goal is to protect users without turning moderation into a surveillance program. Effective moderation balances privacy with safety.
Moderation Strategies That Balance Privacy
- Community standards: Clear rules that explain what is prohibited (hate, threats, doxxing) in plain language. No ambiguity.
- Rate limits and friction: Reduce spam and mass harassment by limiting posting velocity and requiring verified accounts for high-risk actions.
- Reputation signals: Use behavior-based scoring rather than identity-based scoring. A user who consistently contributes valuable content earns trust, even if their name is unknown.
- Escalation paths: Quick action for direct threats and repeated offenders. Slow, careful review for edge cases.
- Human review for edge cases: Automated systems are poor at nuance. Appeals and human decisions prevent over-removal of legitimate speech.
Peer Reporting with Safeguards
Peer reporting is useful, but it can be abused to silence dissent. A strong system uses thresholds (e.g., multiple independent reports from unrelated users), content similarity checks, and transparent action logs. That way, a single malicious report does not take down legitimate voices. The goal is to make the system resistant to gaming while still responsive to genuine harm.
The Role of Protected Identity in Anonymous Content Creation
Protected identity is the difference between “anonymous enough to be safe” and “anonymous enough to be traced.” It is not only about hiding your name; it is about preventing linkability across contexts. This requires a systematic approach to every point of contact between your anonymous and personal selves.
Practical Identity Separation
| Area | Best Practice | Common Mistake |
|---|---|---|
| Accounts | Use separate emails, usernames, and recovery methods. | Using the same email or phone number for recovery. |
| Browsing | Use a dedicated browser profile or device for anonymous work. | Posting from the same browser where you check personal email. |
| Content | Vary posting patterns and avoid repeating specific personal details. | Posting at the same time every day from the same location. |
| Documents | Redact or strip metadata before publishing. | Uploading screenshots with visible filenames or watermarks. |
Mini Case Study: A Creator’s Accidental Leak
A pseudonymous writer felt safe until they posted screenshots of their drafting tool, mistakenly leaving a visible watermark that included their real name. In another case, a creator used the same background wallpaper across anonymous and personal videos, allowing viewers to connect the accounts through visual similarity. The lesson is clear: small, accidental traces can undo even the most careful intentions. Treat every piece of content as a potential clue and audit your output before publishing.
Conclusion
Anonymous and unattributed content is not a loophole or a cheat code. It is a legitimate and often necessary form of expression that requires discipline, foresight, and a strong ethical foundation. Throughout this article, we have explored the full spectrum of what it takes to navigate this realm safely: from understanding the technical threats of IP tracking and device fingerprinting, to implementing practical workflows for secure drafting and publishing, to grappling with the legal and ethical responsibilities that come with speaking without a name.
The key takeaway is that anonymity is not about erasing responsibility; it is about creating a space where expression can be protected without sacrificing trust. When handled with care, unattributed creativity can thrive—safely, intentionally, and with respect for the boundaries that keep people secure. The tools and strategies discussed here, from encryption and metadata removal to protected identity separation and harm-minimization ethics, form a comprehensive framework for anyone serious about this path.
If you are a creator, a community manager, or a digital marketing professional, the principles in this guide are not optional. They are essential for building trust, protecting your audience, and ensuring that your content survives scrutiny. Start by auditing your current practices. Are you leaving traces? Are you assuming more safety than you have? Take one step today: set up a dedicated browser profile for anonymous work, or learn how to strip metadata from your files. The cost of inattention is far higher than the effort of preparation. At our digital marketing agency, we help clients navigate these complexities every day. Contact us to build a content strategy that is both powerful and protected.